
Varonis modules count several solutions such as DatAdvantage (heart of the product) but also Data Classification Engine (for sensitive content discovery and scan) or DatAlert for security analytics to protect your assets.
One of the biggest advantages of DatAlert is to enable you to create custom alerts that you can configure by yourself, which is already great. But DatAlert can also analyze and understand the behaviors of your users to warn you when someone is deviating from its standard behavior (accessing old or unusual data, deleting more documents than usual, etc.).
Introduction
DatAlert can understand many scenarios such as ransomware detection, unusual behaviors from users, and much more. For each alert, you can configure what type of notifications you want to receive: writing in the event viewers or sending them directly to your syslog tool, send a standard email to IT security team but also take some actions! 😉
Yes, that’s mean you can ask DatAlert, when an alert is triggered, to do specific actions thanks to any custom scripts that you will provide to DatAlert. It can be an executable file, bat script or any PowerShell script).
Example
Let’s see how we can do this with a short example. Imagine, you have a specific rule to monitor all the activities in a specific and strategic folder. We will configure this alert to launch automatically a PowerShell script when the alert is detected.
Configuring the alert
In DatAdvantage application, go to Tools and then to DatAlert, DatAlert. Create a new rule or modify any rule already present. Just be sure that you can at least trigger manually your rule to test it at the end of the process. 🙂
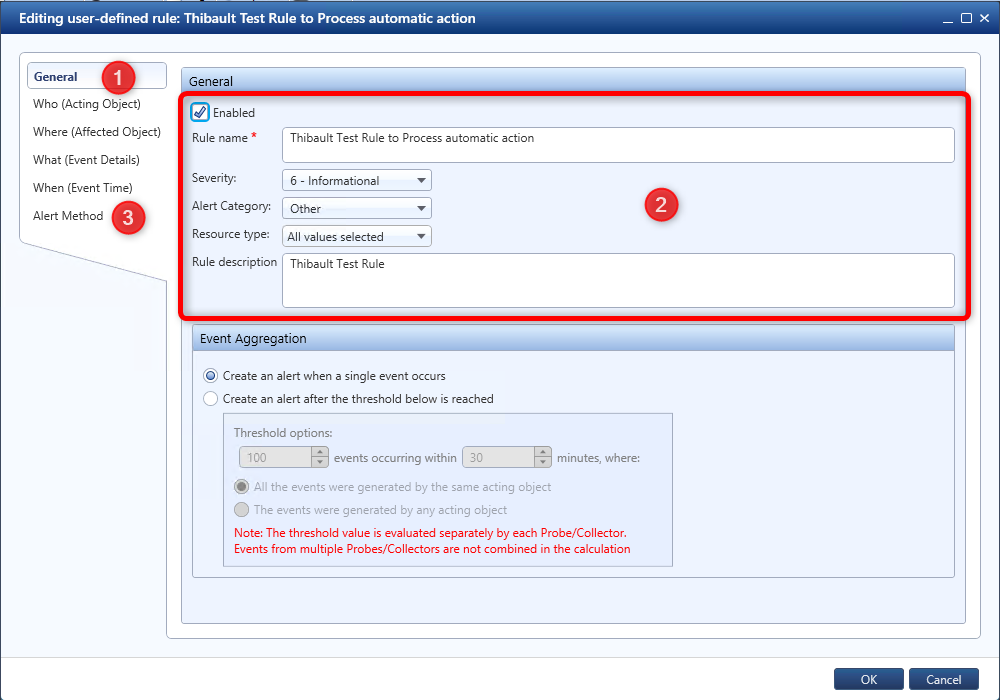
If needed, choose a name, severity, category and a description for your new rule and parameters for Who, What, Where and When tabs. Also note that you should definitively test your rule in a test environment or at least on a reduced perimeter (not on your production environment that could potentially involve ALL your end-users…).
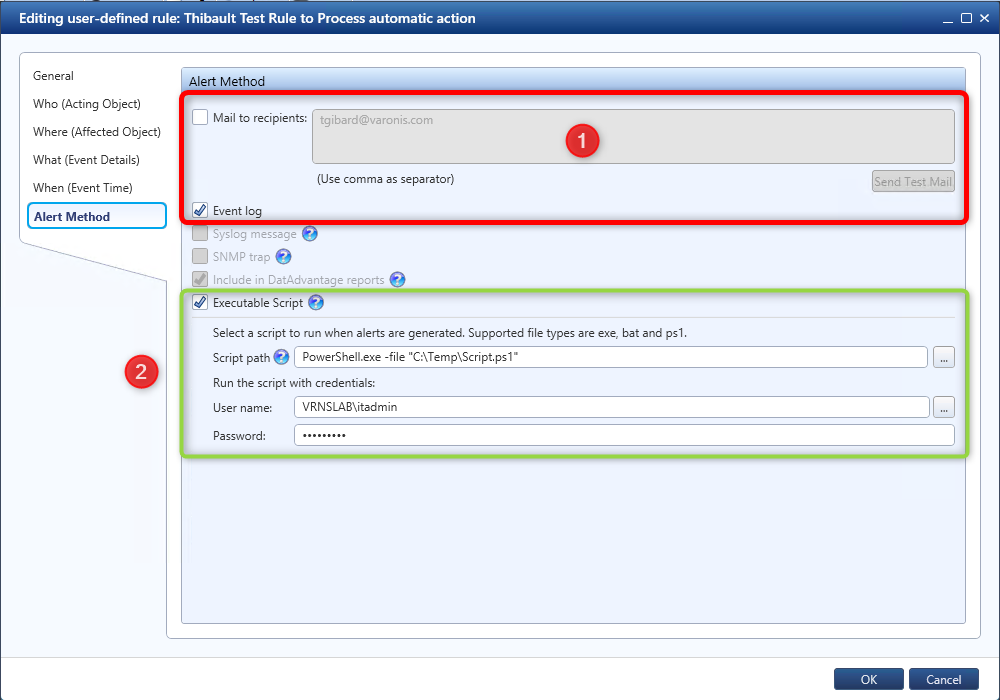
Now go to the Alert Method tab. Normally, it will be in this step that you will configure the type of alert you want receive an email, write in the Event Viewers, etc. But for your test, we want to take some automatic actions! So, check also the option Executable Script.
Be aware that you must store your script on the Varonis Collector that will manage your monitored resource. If you don’t have any Collector, that’s mean you can store the script on your IDU/DSP server. In my example, I’ve saved my script in C:\Temp\Script.ps1 location (very creative). 😉
And here is the interesting part, my script will be composed only of a few lines (yeah, it’s very easy):
# Importing Active Directory CmdLets
Import-Module ActiveDirectory
# Getting variable from Varonis DatAlert
$ActingUser = $env:ActingObjectSAMAccountName
# Processing my action
Disable-ADAccount $actinguser
In my scenario, I just want to disable the concerned Active Directory account of this person because it’s something that can be checked visually after the alert has been triggered.
But as you can see, I’m using specific CmdLet that are provided by Active Directory module. That’s mean, there is no real limitation on the possibilities: I could choose to log off the person, stopping their computer remotely or combine these 2 steps, etc. 🙂
Testing our new Alert
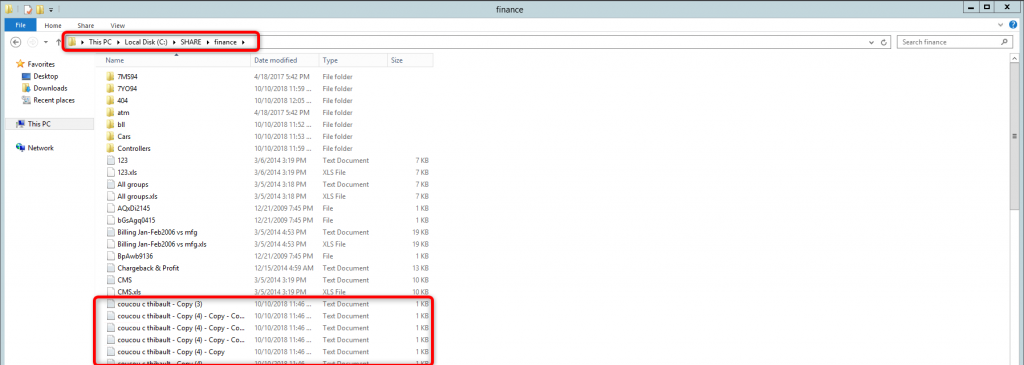
A few minutes before creating my alert, I’ve created plenty of test files in my test monitored folder. Let’s try to remove some of them and see what will happen…
If I’m checking the Event Viewer on my Collector (or IDU) server. I can see my alert has been triggered several times (I’ve deleted several documents in my secret test folder).
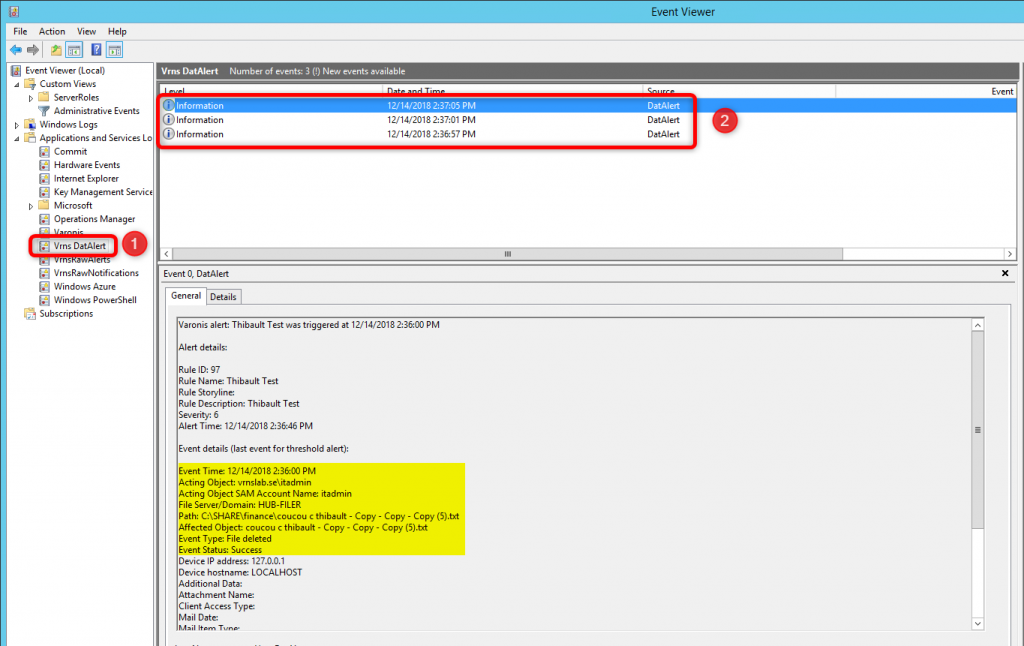
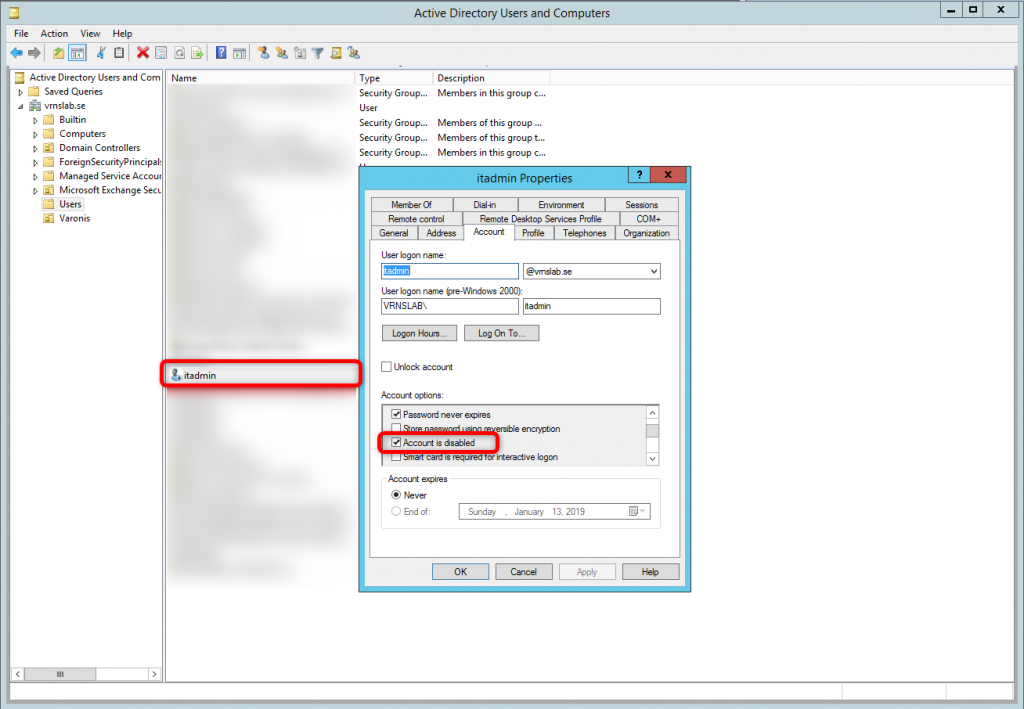
I can see the precise name of the documents which have been deleted, the moment when I’ve deleted them, the name… but more important I can see that the account responsible for this action is « itadmin« .
That’s mean that if my script has worked correctly. This Active Directory account should now be disabled in the AD. Hopefully, this account has been indeed disabled immediately after the first alert. Do not forget that the credentials you’ve used in DatAlert to run the script must be (obviously) allowed to process this action. 😉
Now, think a few minutes about the possibilities. For any monitored actions where you will setup an Alert you can setup specific and automatic answers. That’s mean for example if a ransomware attack is detected you could set up a PowerShell script to disconnect the person, shut down its laptop remotely or maybe shutdown completely the concerned file server?
But there is not only ransomware case. In fact, you can do any actions you want if there is some PowerShell CmdLet available (or any other possibilities to script your actions) when an alert is detected.
Finally, please note that the example in this article is provided « as is », without warranty of any kind, express or implied. You should always test an automatic answer before deploying it to your whole production.










